How to protect yourself from a Frontend Hack?
Frontend Hacks
Frontend attacks have been on the rise recently. We have witnessed Curve and Celer bridge frontends getting hacked.
It usually get detected very fast (few hours on average) but what if you are the first to interact with the malicious contract?
A frontend hack is “an attack in which malicious files are uploaded to the server and then executed, to attack the system”.
Practically speaking, what is a frontend hack in crypto?
You visit Uniswap (everything looks like Uniswap, same website, same UI, etc) but when you interact with the smart contracts on the website and confirm on Metamask, you are actually interacting with malicious contracts which will likely drain your wallet.
It sounds scary but here is a little trick to protect yourself with an example.
Example
Let’s take an example, you want to swap ETH for USDC on Uniswap.
So you go to your favorites and load Uniswap frontend. Then you connect your metamask and you are ready to go for your swap on Ethereum mainnet.
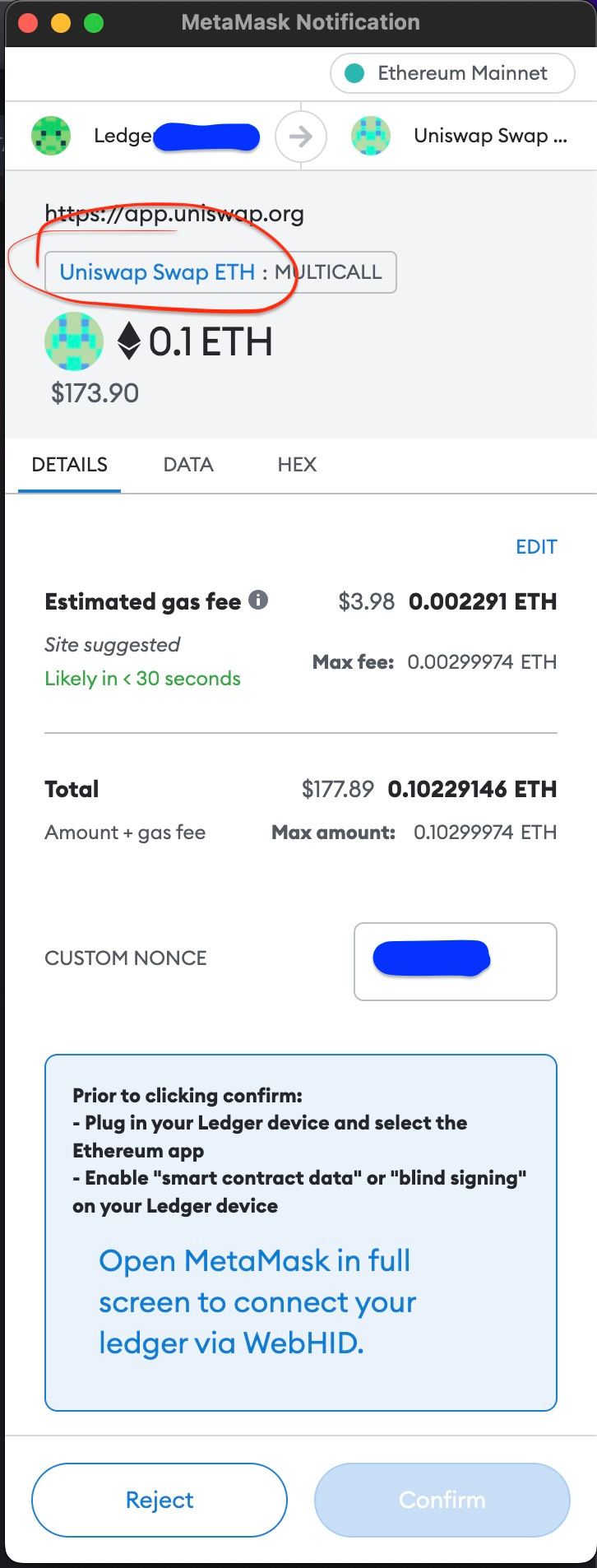
You press swap and metamask pops up asking you to confirm the transaction.
If you did not already changed the nickname of the contract you would have (0x68b3465833fb72A70ecDF485E0e4C7bD8665Fc45 instead of Uniswap Swap ETH).
Personally, I rename the contract as: Name of the dApp, Function, Chain name (ie Uniswap Swap ETH/Ethereum).
Before changing the nickname you ALWAYS HAVE TO DOUBLE CHECK THAT YOU ARE INTERACTING WITH THE RIGHT CONTRACT.
You can always check it by copy pasting the contract address on Etherscan.
If you see that the contract has only a few transactions compared to millions, it is likely that there is an issue with the contract you are viewing. You can always ask the team before transacting.
To change the nickname, nothing more easy, just click on the contract address and edit the nickname.
And save.
Well done Anon! You will never get hacked by a potential Uniswap frontend attack (if you stay focus and verify what you are doing).
Conclusion
Always double check the contract you are interacting with (even more if you don’t know it yet, ie not nicknamed).
You have to edit the nicknames of all the contracts you are interacting with on a weekly basis at least (Uniswap swap, Sushi swap, 1inch, Cowswap, Approve contracts, staking, voting, etc etc etc) to make sure you are interacting only with the official contracts and don’t fall for a frontend hack.
Once you have nicknamed everything in your metamask, you will be less likely to fall for a frontend hack.
Always double check what you are doing before confirming any transactions on your metamask. Avoid getting scammed.
If by mistake you have approved a potentially malicious contract, you can always use revoke.cash to revoke it.
Stay safe!
Secret Salsa
Disclaimer
You understand that no content published on this website or on our social media channels constitute a recommendation to buy or sell any security or cryptocurrency. You acknowledge that the content of this newsletter is for informational purposes only and does not constitute investment advice. Investment in cryptocurrency involves large risks and you are solely responsible of your investment decisions and should consult a financial professional to assess your own personal and financial situation. Secret Salsa is not a registered investment advisor or an investment company.
Secret Salsa attaches a strong importance to accuracy of information provided although it will not hold any responsibility for any missing or wrong information. You understand that you are using any and all information available here at your own risk.